Just After Midnight’s pen testing services offer continuous, strategic and actionable insights.
Rather than a single point-in-time report detailing countless theoretical vulnerabilities, we provide validated attack paths, remediation support, and guidance that can be understood by leadership and actioned by technical stakeholders.
This is to say, penetration testing has moved from handing over a PDF, once, with a low-context list of ‘what ifs’, to a continuous security partnership driven by outcomes.
Here’s how we do it
Just After Midnight’s pen testing process is aligned with a number of industry-standard frameworks built around modern applications.
This means we apply best practices to:
- Application security, via OWASP Web Security Testing Guide (WSTG) and OWASP ASVS
- Cloud security, via CSA Cloud Controls Matrix (CCM)
- API security, via OWASP API Security Top 10
In practice, that means customer journeys will look like:
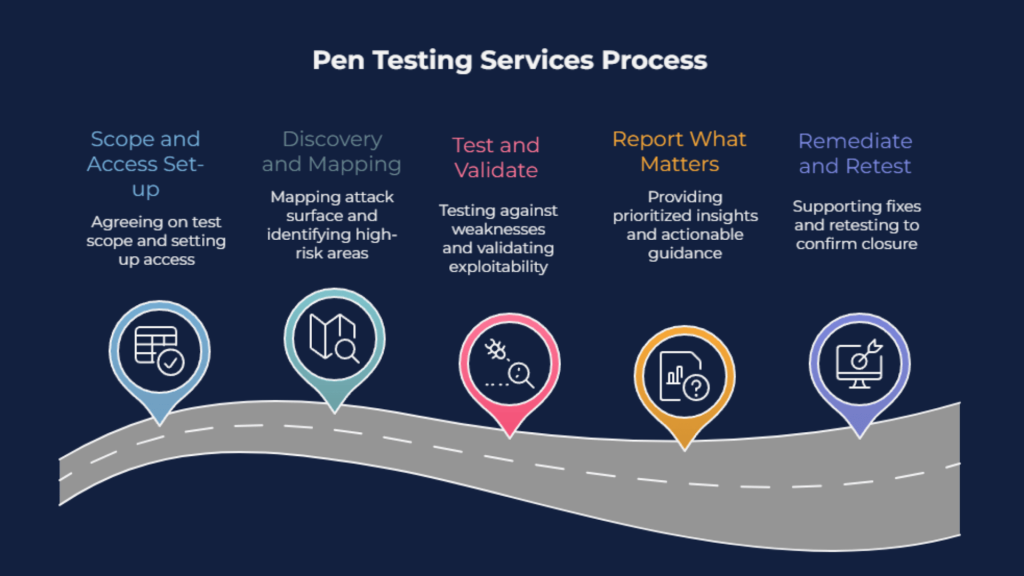
Scope and access set-up
We agree what to test (apps, APIs, cloud services), confirm rules of engagement, and set up the access we need (URLs, test accounts, environments).
Discovery and mapping
We map your attack surface and key user journeys/endpoints, then define the highest-risk areas to focus on (auth, access control, data flows, cloud permissions).
Test and validate
We test against common and high-impact weaknesses across application security, API security, and cloud configuration, and validate what’s genuinely exploitable.
Report what matters
You get prioritised, actionable insights: validated attack paths, real-world impact, and fix-ready guidance for engineers, plus a clear summary for leadership.
Remediate and retest
We support your team as fixes are implemented, then retest to confirm closure and document the outcome.
All of the above is delivered aligned within the relevant framework, and with full visibility: as the picture evolves, you’ll be the first to know.
The outcomes we deliver
Protecting your business from breaches means:
- Predictable operations and service continuity
- Better decision-making and governance
- Faster innovation
Vulnerabilities ultimately expose you to risk, force you to plan around risk, and to bear the opportunity cost of lost time.
With nearly half of UK businesses affected by breaches, and similar numbers in the US and APAC, this is a problem costing businesses the world over revenue, reputation and reliability.
So, why not join the other half.
How we can help
As a global, next-gen MSP, we help everyone from start-ups to enterprises gain clear, actionable security insights.
We work with senior stakeholders and technical teams to align remediation with business objectives and free organisations from the costs of risk.
To find out how we could help you, just get in touch.